Blog

How to Improve the Security of TNAS
The security of data is very essential to everyone. To improve the security of TNAS and prevent data loss, we can take some measures. Here are some solutions. 1. Upgrade...
How to Improve the Security of TNAS
The security of data is very essential to everyone. To improve the security of TNAS and prevent data loss, we can take some measures. Here are some solutions. 1. Upgrade...

Efficient Cloud Disk Disaster Recovery Solution
What is CloudSync? CloudSync is a cloud drive synchronization application that facilitates fast and secure data synchronization between the TNAS and relevant cloud drives. It is thus a very practical...
Efficient Cloud Disk Disaster Recovery Solution
What is CloudSync? CloudSync is a cloud drive synchronization application that facilitates fast and secure data synchronization between the TNAS and relevant cloud drives. It is thus a very practical...

How to Build Your Own Private Cloud Disk?
Public cloud disk is a professional Internet storage tool and a product of Internet cloud technology. It provides information storage, reading, downloading and other services for enterprises and individuals through...
How to Build Your Own Private Cloud Disk?
Public cloud disk is a professional Internet storage tool and a product of Internet cloud technology. It provides information storage, reading, downloading and other services for enterprises and individuals through...

Complete Picture Management Solution for TNAS U...
In the digital age, people are used to taking pictures anytime and anywhere to record wonderful moments. After a long time, the number of accumulated pictures must be very large...
Complete Picture Management Solution for TNAS Users
In the digital age, people are used to taking pictures anytime and anywhere to record wonderful moments. After a long time, the number of accumulated pictures must be very large...

Improved Virtualization Application of TNAS
iSCSI, short from Internet Small Computer System Interface, also known as IP-SAN, is a storage technology based on the Internet and the SCSI-3 protocol. iSCSI uses TCP/IP ports 860 and...
Improved Virtualization Application of TNAS
iSCSI, short from Internet Small Computer System Interface, also known as IP-SAN, is a storage technology based on the Internet and the SCSI-3 protocol. iSCSI uses TCP/IP ports 860 and...

High Efficient Surveillance Solution with TNAS
From home to business, the application of video surveillance is more and more extensive. Home video surveillance provides visibility into your home anytime, anywhere; enterprise video surveillance protects corporate assets...
High Efficient Surveillance Solution with TNAS
From home to business, the application of video surveillance is more and more extensive. Home video surveillance provides visibility into your home anytime, anywhere; enterprise video surveillance protects corporate assets...

Easy-To-Use VPN Solution with TNAS
The full name of VPN in English is "Virtual Private Network". A VPN is defined as a temporary, secure connection through a public network (usually the Internet), a secure, stable...
Easy-To-Use VPN Solution with TNAS
The full name of VPN in English is "Virtual Private Network". A VPN is defined as a temporary, secure connection through a public network (usually the Internet), a secure, stable...

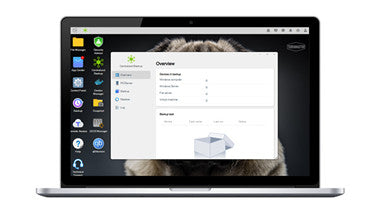
New USB Management Tools
To facilitate the management of USB devices, TOS 5 adds even more USB management tools. USB permission control Using the new USB permission control, administrators can designate which users have...
New USB Management Tools
To facilitate the management of USB devices, TOS 5 adds even more USB management tools. USB permission control Using the new USB permission control, administrators can designate which users have...

New Duple Backup-Disaster Recovery Solution for...
For all walks of life, data is the core and most important wealth, but natural and man-made disasters such as fires, earthquakes, hacker attacks, and human misoperations threaten the stable...
New Duple Backup-Disaster Recovery Solution for TNAS
For all walks of life, data is the core and most important wealth, but natural and man-made disasters such as fires, earthquakes, hacker attacks, and human misoperations threaten the stable...

How to Use TerraMaster NAS to Build a 2.5GbE an...
At present, people's requirements for data storage and transmission speed are getting higher and higher, enterprises also have new requirements for network bandwidth, and the speed of network cards is...
How to Use TerraMaster NAS to Build a 2.5GbE and 10GbE High-Speed Network Env...
At present, people's requirements for data storage and transmission speed are getting higher and higher, enterprises also have new requirements for network bandwidth, and the speed of network cards is...
How to Prevent Data Tampering?
Data is a precious asset for almost all users, and data security is very important to everyone. Some data storage requirements are also regulated by law, as seen in court...
How to Prevent Data Tampering?
Data is a precious asset for almost all users, and data security is very important to everyone. Some data storage requirements are also regulated by law, as seen in court...

Ransomware? TOS 5 Comes with Higher Security
Hackers and ransomware merchants are a large problem currently around the world, and a large number of precious digital assets are thus under unprecedented threat. For network security issues, people...
Ransomware? TOS 5 Comes with Higher Security
Hackers and ransomware merchants are a large problem currently around the world, and a large number of precious digital assets are thus under unprecedented threat. For network security issues, people...

What's the OTP Authorization Function in TOS 5?
One-time password (OTP) systems provide a mechanism for logging on to a network or service using a unique password that can only be used once. The OTP feature prevents certain...
What's the OTP Authorization Function in TOS 5?
One-time password (OTP) systems provide a mechanism for logging on to a network or service using a unique password that can only be used once. The OTP feature prevents certain...
How to quickly find the target file in the mass...
There is no doubt about the importance of data, and the common sense of data storage is also widely recognized. Therefore, the capacity of stored data is becoming larger and...
How to quickly find the target file in the massive database?
There is no doubt about the importance of data, and the common sense of data storage is also widely recognized. Therefore, the capacity of stored data is becoming larger and...

How to choose a disaster recovery tool?
As long as there is data transmission, data storage and data exchange, there will be risks such as data failure, data loss, and data damage, due to natural or man-made...
How to choose a disaster recovery tool?
As long as there is data transmission, data storage and data exchange, there will be risks such as data failure, data loss, and data damage, due to natural or man-made...
Mirror backup, can only choose RAID 1?
When it comes to mirror data backup, most people will mention RAID 1. RAID 1 realizes data redundancy through disk data mirroring, and generates mutually backup data on pairs of...
Mirror backup, can only choose RAID 1?
When it comes to mirror data backup, most people will mention RAID 1. RAID 1 realizes data redundancy through disk data mirroring, and generates mutually backup data on pairs of...
How do Enterprises Efficiently Backup Data?
For enterprises and organizations, it is easy to find any computer system may crash; anyone may make mistakes; disasters always seem to happen when they least expect it. Therefore, data...
How do Enterprises Efficiently Backup Data?
For enterprises and organizations, it is easy to find any computer system may crash; anyone may make mistakes; disasters always seem to happen when they least expect it. Therefore, data...
TRAID-Flexible Disk Array Management Tool
For groups familiar with NAS devices, when it comes to data protection, the first thing that comes to mind may be setting up RAID. Indeed, RAID technology has made outstanding...
TRAID-Flexible Disk Array Management Tool
For groups familiar with NAS devices, when it comes to data protection, the first thing that comes to mind may be setting up RAID. Indeed, RAID technology has made outstanding...

TNAS Video Surveillance Management Application
TNAS video surveillance management application refers to an application in the TOS system - Surveillance Manager, which users can use in systems above 4.2. Surveillance Manager actually is a video...
TNAS Video Surveillance Management Application
TNAS video surveillance management application refers to an application in the TOS system - Surveillance Manager, which users can use in systems above 4.2. Surveillance Manager actually is a video...

What is VPN and its Applications
VPN, which means "Virtual Private Network," is a service that protects your Internet connection as well as your online privacy. By hiding your IP address, this service will create an...
What is VPN and its Applications
VPN, which means "Virtual Private Network," is a service that protects your Internet connection as well as your online privacy. By hiding your IP address, this service will create an...

DNS over HTTPS: Internet Privacy
What’s DNS? The first is the DNS side of DNS over HTTPS. DNS comes into play when you type a URL into your browser's address bar. For example, we might...
DNS over HTTPS: Internet Privacy
What’s DNS? The first is the DNS side of DNS over HTTPS. DNS comes into play when you type a URL into your browser's address bar. For example, we might...
